Twingate and Tailscale both provide secure remote access without traditional VPNs. They take different approaches: Twingate is built around zero-trust resource access, while Tailscale creates a mesh network where devices can talk to each other. This article outlines what each platform does and where they diverge, so you can see which fits your needs.
Twingate is a zero-trust remote access platform that gives users access to specific resources - hosts or applications identified by FQDN or IP - rather than entire networks. You deploy connectors in your private networks; they maintain outbound-only connections to Twingate's cloud control plane, so no inbound ports are required. Users connect to resources by FQDN or IP; the system handles routing and encryption over proprietary TLS-based tunnels, using direct peer-to-peer connections when possible and relaying through Twingate's infrastructure when not.
The model is resource-centric: you define specific applications, databases, or servers as Resources in the dashboard. You then grant users or groups access to specific Resources. Users install the Twingate client, sign in, and see only what they are authorized to access. Access is deny-by-default. Twingate is closed source and operates as a cloud-hosted, multi-tenant service. You do not self-host the control plane (called the Controller).
Tailscale is a mesh-based overlay VPN service built on WireGuard. It creates a private network, called a tailnet, where your devices can talk to each other over the internet as if they were on the same LAN.
Devices join the tailnet by running the Tailscale client. Each device gets an IP address on the overlay network. Once connected, devices can reach each other directly using those IPs. Tailscale uses NAT hole punching and WireGuard key exchange so devices can form direct links through firewalls without opening ports; when direct connections fail, traffic relays through Tailscale's DERP (Designated Encrypted Relay for Packets) infrastructure.
Tailscale is built for device-to-device and server-to-server connectivity. The mental model is "devices on a shared private network" rather than "users accessing specific resources." You control who can reach what using ACLs (access control lists) written in JSON. Tailscale runs as a cloud-only service with their hosted control plane. A community project called Headscale reimplements the Tailscale control plane for self-hosting, but it is not an official Tailscale product and requires you to maintain it yourself.
The table below summarizes the main differences. The sections after it walk through each area in order.
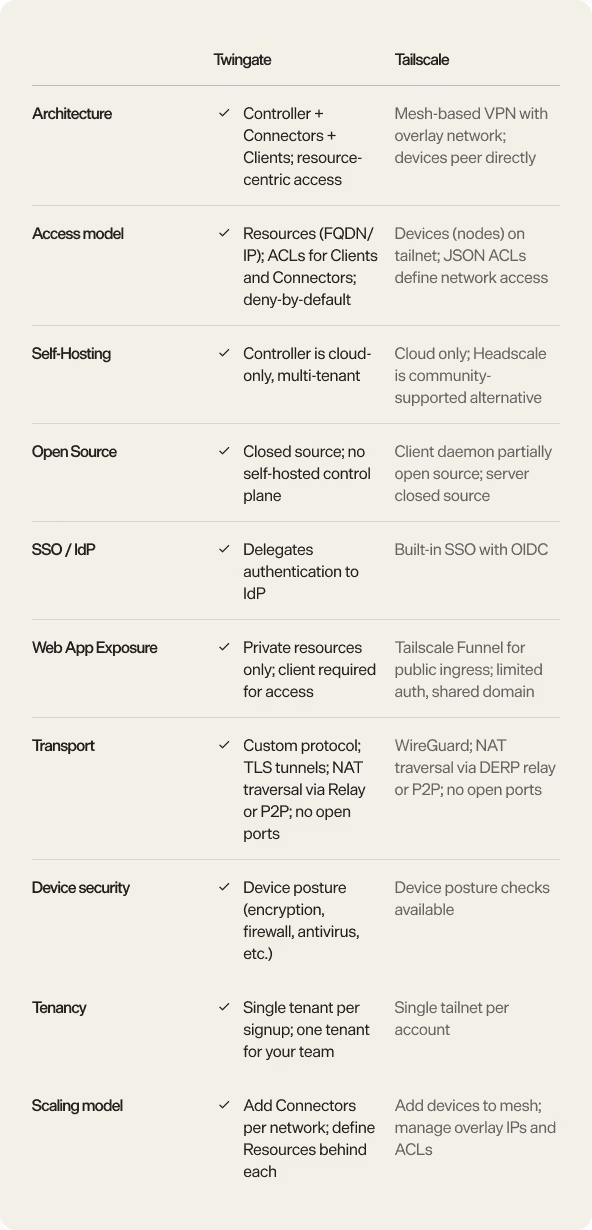
Twingate and Tailscale use fundamentally different architectures to solve remote access.
Twingate uses a connector-based, hub-and-spoke model. Connectors run in your private networks and maintain outbound-only connections to the cloud. When a user wants to access a Resource, their client connects directly to a Connector (peer-to-peer when possible, or via Twingate's relay when NAT traversal fails). Clients do not talk to each other; they only reach the Resources you have granted them access to. This keeps the model simple: you scale by adding Connectors to new networks and defining Resources behind them.
Tailscale uses a full mesh architecture. Every device in the tailnet can form direct WireGuard links to every other device. Data flows peer-to-peer when possible; when direct connections fail, traffic routes through Tailscale's DERP relay servers. The network model is "all devices on one virtual network" (subject to ACLs). This works well for small to medium sets of devices that need to talk to each other. At larger scale, managing the mesh topology, overlay IP space, and ACL complexity grows with the number of devices.
Twingate organizes access around resources: specific applications, hosts, or services identified by FQDN or IP. Admins define Resources in the dashboard and grant users or groups access to them. Users install the Twingate client, sign in, and see only the Resources they are authorized to use. Access is deny-by-default: nothing is reachable until you explicitly grant it. Sessions are per Resource, and the client handles routing transparently. Twingate also supports service accounts for machine-to-machine access - servers, CI/CD pipelines, and other non-interactive systems that need to reach private Resources.
Tailscale organizes access around devices (nodes) on a tailnet. You install the client on each device that should join the network. Each device gets an overlay IP address (typically in the 100.x.x.x CGNAT range). ACLs define which nodes (or tags) can reach which other nodes, subnets, or ports. The unit of access is the device or subnet, not a named application. It is powerful for network-level control, but less direct for "grant this user access to this specific app" without thinking in terms of IPs, ports, and device tags.
Twingate provides a dashboard to define who can access which Resources. You grant access to users and groups. Twingate delegates authentication to your identity provider (Okta, Azure AD, Google Workspace, and others). The system manages who can access what and pushes this to Clients and Connectors; you do not edit ACLs by hand. Twingate also supports device posture checks: you can require that devices have disk encryption enabled, a firewall running, antivirus up to date, and similar security settings before granting access. Policies are resource-centric: "this group can access this database" or "these users can reach this internal API."
Tailscale uses JSON ACLs written in a policy file. You define rules that allow or deny traffic between nodes, by tag, user, or to specific ports and subnets. It is network-centric: you think in terms of IP ranges, ports, and device tags. Tailscale also supports SSO via OIDC and device posture checks (called device authorization). The main lever for access control is the ACL file, which you edit in the Tailscale admin console or manage via gitops. It gives you fine-grained networking control, but it is less intuitive for application-level access policies like "grant this person access to Grafana."
Twingate is built for private Resource access. All access requires the Twingate client installed on the user's device. There is no built-in, clientless browser path for web applications. If you need users to access internal web apps, they must install the client first. Twingate does not function as an identity-aware reverse proxy with custom domains and public URLs for web resources.
Tailscale offers Tailscale Funnel for exposing services from your tailnet to the public internet. Funnel lets you route public HTTPS traffic through the tailnet to a local service without opening ports. However, Funnel has limitations for web app access: authentication options are limited (primarily tailnet member access or fully public), and all Funnel resources share the same base domain (e.g., *.ts.net) - you control only the subdomain, not the full domain. Funnel is not designed as a full identity-based reverse proxy for internal web apps with strong authentication, custom domains, and per-resource access control. It is more akin to a quick way to expose a service publicly, similar to ngrok or Cloudflare Tunnel, but with less emphasis on identity and access management.
Neither platform offers the same level of clientless, identity-aware web access that a platform like Pangolin provides (see below).
Twingate operates as a cloud-hosted service. The Controller (control plane) is managed by Twingate; you do not self-host it. Connectors run in your infrastructure (on-premises, cloud VPCs, etc.), and you can optionally deploy your own relay nodes to keep data traffic on your infrastructure. However, the control plane - where configuration, ACLs, and user data live - remains cloud-only. If you require the entire control plane and all metadata to run on your own infrastructure, Twingate does not offer that option.
Tailscale also operates as a cloud-only service. You depend on Tailscale's hosted coordination server and DERP relay infrastructure. Tailscale's client daemon (tailscaled) is partially open source, but the coordination server is proprietary. Headscale is a community-built, open-source implementation of the Tailscale coordination server. Some teams use Headscale to self-host the control plane, but you are responsible for deploying, maintaining, and operating it. It is not an official Tailscale product, and it may lag behind Tailscale's feature set. You can also self-host DERP relay nodes to keep traffic off Tailscale's infrastructure, but the coordination server remains cloud-only unless you use Headscale.
Twingate uses a connector-per-network model. You deploy one Connector (or a few for redundancy) in each private network or segment. You then define Resources - specific hosts, applications, or services - behind that Connector. Users can have access to Resources across multiple networks simultaneously. The Connector handles routing to those Resources. This model scales by adding Connectors and Resources. You do not maintain a large overlay IP space, and you do not manage peer-to-peer connections between all devices. If you have two cloud VPCs - one with production databases and one with staging servers - you deploy two Connectors and define Resources in each. Users connect to the Connectors, not to individual servers. The operational complexity is linear: more networks mean more Connectors, but not exponentially more connections or ACL entries.
Tailscale uses a device-per-node model. Each device you want to access must either run the Tailscale client. In the same two-VPC scenario, you would install the Tailscale client on every database server and virtual machine you want to access. This becomes more complex in large deployments with many resources, especially for resources that cannot run the Tailscale client - like managed databases, appliances, or services where you do not control the OS. Each device gets an overlay IP address (typically in the 100.x.x.x range), and you manage that address space as the tailnet grows. You also manage ACLs that define which nodes can reach which other nodes or subnets. At large scale, the mesh and ACL complexity can grow significantly: adding more devices means more peer relationships, more overlay IPs to track, and longer ACL files.
Both platforms support device posture checks: gathering information about security settings on user devices. This includes whether disk encryption is enabled, the firewall is on, antivirus is present and up to date, OS version, and similar. You can use posture data in access policies to allow or deny access based on device security state.
Twingate enforces posture checks on a per-Resource basis. You can require that a device meets certain security criteria before it can access a Resource. Twingate also supports device fingerprinting: collecting device-specific identifiers like serial numbers and hardware information to recognize and track devices over time.
Tailscale offers device posture through its device authorization feature. You can require that devices meet posture requirements to join the tailnet or access certain nodes. Posture checks are enforced at the tailnet level or via ACL rules.
Twingate is single-tenant. When you sign up, you get one tenant for your organization. Managing multiple separate organizations (e.g., as an MSP serving many customers) requires separate Twingate accounts or using their special MSP service and is less natural than a multi-org model.
Tailscale is also single-tenant by default: one tailnet per account. Tailscale does offer a feature for larger organizations to create multiple tailnets under one umbrella, but the primary model is one tailnet for one team or organization.
Twingate is fully closed source. You cannot inspect, modify, or self-host the Controller or any part of the platform. The entire stack - clients, Connectors, Controller, and relays - is proprietary.
Tailscale has a partially open-source model. The Tailscale client daemon (tailscaled) and some libraries are open source. Full client applications (mobile apps, GUI apps) and the coordination server are proprietary. You cannot self-host the official Tailscale coordination server. Headscale is an independent, open-source reimplementation of the coordination server that you can self-host, but it is maintained by the community and may not have feature parity with Tailscale's official service.
Choose Twingate if you want zero-trust, resource-centric access where you grant users access to specific applications, databases, or servers - not entire networks. Twingate fits organizations that think in terms of "who can access which internal app or service" and want a system that enforces deny-by-default access without requiring users to understand networking. It is a good fit if you are comfortable with a cloud-only control plane and do not need clientless web access or self-hosting the control plane.
Choose Tailscale if you want a simple mesh VPN where devices and servers can talk to each other as if on a private LAN. Tailscale fits small to medium deployments where device-to-device or server-to-server connectivity is the main goal, and you are comfortable expressing access policy in JSON ACLs. It works well when you control the devices and can install the Tailscale client on them. Tailscale is also a good fit if you value the WireGuard protocol and want a service that is partially open source, with the option to use Headscale for self-hosting the control plane if needed.
If you are evaluating Twingate for zero-trust, resource-centric access but want more flexibility or control, Pangolin is worth considering.
Like Twingate, Pangolin uses a connector-based model (Pangolin calls them sites). You deploy lightweight connectors in your networks, define resources (web apps, databases, SSH hosts, APIs), and grant users access to specific resources. Access is deny-by-default. Clients connect directly to sites, not to each other.
Where Pangolin differs:
Open source and self-hostable: Pangolin's server and clients are fully open source (AGPLv3 or Commercial License). You can self-host the entire platform if you need full control over the control plane and data. Alternatively, use Pangolin Cloud and optionally deploy your own relay nodes to keep traffic on your infrastructure.
Clientless web access: Pangolin can expose web applications without a client. Users open a URL, sign in (e.g., with SSO), and reach the app in the browser. Pangolin can act as an identity-aware reverse proxy with automatic SSL certificates, custom domains, and layered authentication (pin codes, passcodes, user auth, email whitelists) in addition to VPN capabilities. This fits contractors, BYOD, or quick access to internal tools without installing software.
Built on WireGuard: Pangolin uses the same proven, open-source WireGuard protocol that Tailscale is built on, not a proprietary transport.
Multi-tenancy: Pangolin supports multiple organizations under one account. You can share users and resources across organizations, making it well suited for MSPs or teams managing multiple customers.
Pangolin combines the resource-centric, zero-trust model of Twingate with clientless web access, full self-hosting options, and the transparency and flexibility of open source. If those capabilities matter to you, Pangolin is a strong alternative.
Get started with Pangolin. You can self-host the server or sign up for the cloud and try it with no commitment.
If you want more detail on how Pangolin compares to Twingate or Tailscale for your specific setup, reach out.