The comparison between Pangolin and WireGuard often misses a key distinction. While WireGuard is a superb, high-performance Layer 3 tunnel protocol, it functions purely as a secure network interface, not a complete remote access solution. Pangolin, however, is a full remote access platform that uses WireGuard as its foundation. It builds upon WireGuard by integrating essential features for real-world secure deployment, including identity management, policy enforcement, automation, and a user experience that doesn't demand specialized networking knowledge.
If you appreciate WireGuard, you will find Pangolin an ideal solution. It allows you to manage access at scale without the time and effort required to build the missing platform layer yourself.
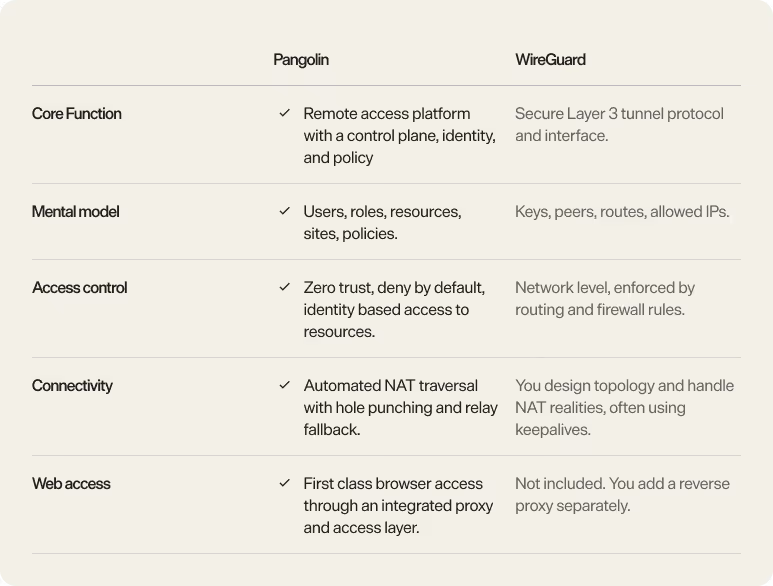
WireGuard is intentionally simple. You create a virtual interface, exchange public keys, define which IP ranges are routed through the tunnel, and bring the interface up. It gives you a strong foundation that is small, auditable, and fast.
That simplicity is also where most teams feel the friction. WireGuard’s model is “cryptokey routing”. You associate a peer public key with what it is allowed to reach, and everything else depends on the system you build around those primitives.
For small setups, WireGuard's simplicity, often likened to exchanging SSH keys, holds true.
However, the complexity escalates significantly with larger deployments involving numerous users, multiple sites, external contractors, frequent device changes, and the requirement for auditable security from a dedicated team. In these scenarios, WireGuard lacks essential features such as an enrollment workflow, an identity directory, or a robust policy engine. Organizations are left to manually manage key issuance, device approval, and, critically, access revocation across all locations where peer configurations are defined.
Consequently, many WireGuard implementations quickly evolve into unmanaged "DIY access control" systems.
WireGuard long term keys live wherever your configuration lives. That might be on endpoints as configuration files, in automation tooling, in a password manager, or in a configuration repository. The protocol is secure, but your security posture is now strongly influenced by how well you manage secret sprawl and configuration drift.
Common failure modes include:
WireGuard does not know what an “employee”, “contractor”, “database”, or “admin panel” is. It moves packets. Least privilege is possible, but you implement it using routing, IP plans, and firewalls, and you must keep those rules correct over time.
In practice, this is why WireGuard deployments often start narrowly and then drift toward broader access than intended as exceptions pile up.
WireGuard is silent when idle by design. In NAT heavy environments, peers may require persistent keepalives to maintain inbound reachability. This is a normal trade off of keeping the protocol minimal, but it pushes deployment complexity up into operations.
The result is a familiar set of issues: a peer works at home but not on hotel Wi Fi, it works on one mobile network but not another, or it requires additional infrastructure like hubs and jump hosts to provide consistent connectivity.
WireGuard is powerful, but it is a building block. It gives you a fast encrypted tunnel. It leaves key distribution, lifecycle management, policy design, NAT traversal strategy, and day two operations to you.
Pangolin’s value is that it turns WireGuard from a great tunnel into a complete access product. Pangolin is a zero trust access platform built on WireGuard. It shifts the model away from IP level plumbing and toward users, roles, and resources.
Instead of treating every peer configuration as a hand crafted artefact, Pangolin introduces a control plane that coordinates connectivity and access. The architecture includes a control plane with a web interface, API, authentication, a database, and WebSocket coordination, plus components that manage WireGuard tunnels and connectivity.
Pangolin offers a client credential model that streamlines operations by eliminating the need to distribute static peer configurations across an organization. Clients first set up a control channel and then use ephemeral keys to establish their WireGuard tunnels.
The practical benefit is straightforward: teams stop spending time managing peer files and start managing access policy.
Pangolin’s resource model is explicit: access must be granted to users, roles, or machines for a WireGuard tunnel to be established to the site hosting the resource. The default posture is denied by default.
Instead of giving someone a tunnel into a network and hoping firewall rules stay perfect, Pangolin encourages a safer model: define the resources that matter, then grant access to those resources based on identity.
This aligns with how organisations actually think about risk. People need access to a database, an internal dashboard, or a subnet used by a staging environment. They rarely need unrestricted network presence.
Pangolin directly addresses the real world mess of NAT and firewalls.
Pangolin implements a two-stage connectivity strategy. It initially tries to achieve direct peer-to-peer connection using NAT hole punching. If a direct path fails, it reverts to relaying traffic via Gerbil. Critically, this relay forwards WireGuard packets while maintaining the integrity of the end-to-end WireGuard encryption.
This enhancement shifts the user experience from a dependence on network conditions, where "the VPN sometimes works," to an automatic resolution where "the client finds a working path." The benefit is a reduced need for users to implement manual network adjustments and fragile workarounds.
WireGuard does not include web access. Pangolin includes a reverse proxy and middleware layer that provides browser based access for public resources, integrated with the same identity and access control system.
This is a major difference for teams that want a single system for both web applications and private TCP or UDP services.
Pangolin offers a more advanced operational framework than Wireguard. This framework is built around concepts such as sites and resources, and features deployment and configuration workflows optimized for continuous management, rather than focusing solely on a one-time initial setup.
The fundamental difference between Pangolin and WireGuard is the scope of their features.
WireGuard is celebrated for its elegance and minimalism. It is the ideal choice for environments with simple network topologies where an organization prefers to manage and build its own custom access system around a core tunneling protocol.
Pangolin, by contrast, provides a more comprehensive platform. While this means introducing more components and complexity, it integrates many features that most teams ultimately need to develop internally: Identity-based access policies, default-deny resource access control, automatic NAT traversal with relay as a backup, and built-in web access.
For the majority of organizations, this comprehensive trade-off is beneficial. Pangolin utilizes WireGuard's high-level security and performance characteristics at the transport layer, but extends them with a platform layer that creates a truly scalable, usable access solution.